The modern software development lifecycle (SDLC) relies heavily on dependency management. Tools like Composer are the backbone of the PHP ecosystem, allowing developers to pull in thousands of external packages effortlessly. However, this convenience introduces a massive attack surface.
When critical vulnerabilities surface, such as the recent wave of PHP Composer Flaws enabling arbitrary command execution, the entire industry must pause and reassess its dependency hygiene. These flaws are not merely theoretical; they represent a direct threat to the integrity of the build process itself.
This deep dive is designed for Senior DevOps, SecOps, and MLOps engineers. We will move beyond simply patching versions. Instead, we will architect a resilient, multi-layered defense strategy to ensure that even if a dependency contains a flaw, your production environment remains isolated and secure.
Table of Contents
Phase 1: Understanding the Attack Surface and Core Architecture
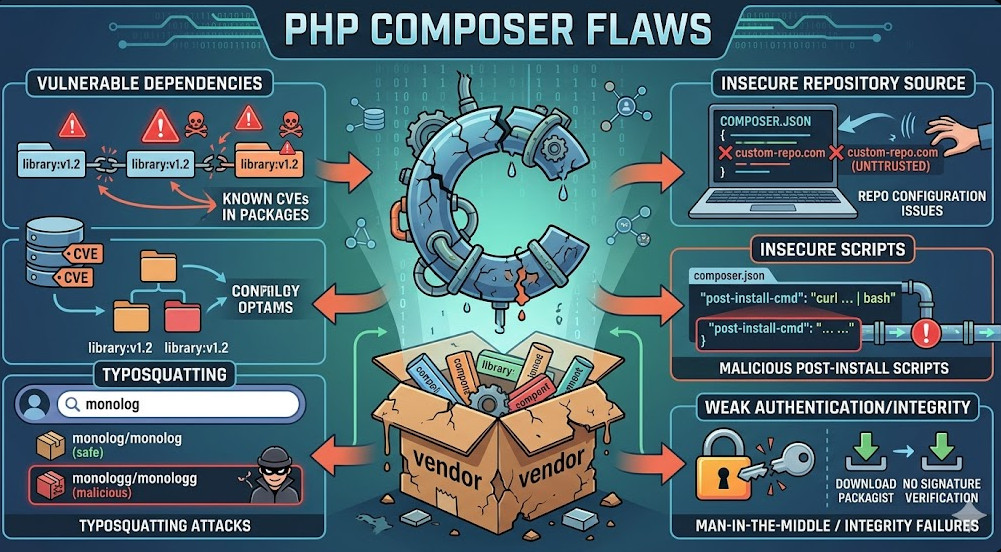
To defend against PHP Composer Flaws, you must first understand the mechanisms by which they operate. The primary threat vector is the exploitation of the dependency resolution process, often leading to Supply Chain Attacks.
The Role of Composer and the Risk of Arbitrary Execution
Composer is fundamentally a package manager, but its power—and its risk—lies in its ability to execute scripts defined within the packages it installs. Many packages include scripts sections in their composer.json, allowing them to run pre-install, post-install, or even pre-update hooks.
If a malicious or flawed package is introduced, an attacker can exploit these hooks to execute arbitrary commands on the build machine. This is the core mechanism behind many PHP Composer Flaws. The goal is often to achieve Remote Code Execution (RCE), allowing the attacker to steal secrets, modify code, or exfiltrate data.
Architectural Deep Dive: The Principle of Least Privilege
Securing the build process requires adopting the Principle of Least Privilege (PoLP) at every stage. This means that the CI/CD runner, the build container, and the deployment user should only possess the minimum permissions necessary to complete their single, defined task.
When dealing with dependency management, PoLP dictates that the build environment should never have direct access to production secrets or the ability to write outside of designated, ephemeral directories.
Key Architectural Mitigation Points:
- Ephemeral Build Environments: Every build must run in a clean, disposable container (e.g., Docker). This ensures that any malicious payload executed during the build cannot persist or affect subsequent builds.
- Read-Only Filesystems: The core application code and the installed vendor directory should be mounted as read-only where possible, limiting the scope of damage if a flaw is exploited.
- Network Segmentation: The build runner should be network-isolated, preventing outbound connections to suspicious IPs or internal corporate networks that are not strictly required for package fetching.
Phase 2: Practical Implementation – Hardening the Dependency Graph
Mitigating PHP Composer Flaws is not a single patch; it is a rigorous process of dependency graph management and pipeline hardening. We must enforce strict controls over what gets installed and how it is executed.
Step 1: Locking Dependencies and Version Pinning
The most immediate and crucial step is to move away from relying solely on loose version constraints (^1.0 or *). These constraints allow Composer to pull the latest version, which could contain a newly discovered flaw.
You must commit and strictly enforce the composer.lock file. This file records the exact version and hash of every single dependency that was successfully installed during a known-good build.
Example: Enforcing the Lock File
When running Composer in CI/CD, always use the --no-dev and --optimize-autoload flags, and critically, ensure the lock file is present.
# In CI/CD pipeline script (e.g., Jenkinsfile or GitHub Actions)
composer install --no-dev --optimize-autoload --no-interaction
Step 2: Implementing Dependency Scanning and Vetting
Relying solely on composer.lock is insufficient because it only guarantees the current state. You need continuous monitoring.
Integrate automated dependency scanning tools (like Snyk, Dependabot, or specialized commercial tools) directly into your Git pre-commit or pull request workflow. These tools analyze the composer.lock against known vulnerability databases (CVEs).
💡 Pro Tip: Don’t just scan for known CVEs. Implement a policy that flags any package that has recently changed its maintainer or has a high rate of dependency updates. This helps detect potential PHP Composer Flaws before they are officially cataloged.
Step 3: Restricting Composer Script Execution
Since the vulnerability often lies in the execution of scripts, you must audit and restrict them.
- Audit: Review the
scriptssection of every package listed in yourcomposer.json. - Minimize: Only keep scripts that are absolutely necessary for the build process (e.g.,
post-autoload-dump). - Isolate: If a script must run, ensure it executes within a highly restricted sandbox environment, limiting its syscall capabilities.
Example: Minimalist composer.json
A hardened composer.json should be as minimal as possible, only listing direct, critical dependencies.
# composer.json
name: my/secure-app
description: Highly secure application
require:
php: ^8.2
monolog/monolog: ^2.0
symfony/yaml: ^6.0
# Avoid listing dependencies that require complex scripts if possible.
Phase 3: Senior-Level Best Practices and Runtime Defense
The best defense against PHP Composer Flaws is assuming that a flaw will be exploited. Your architecture must therefore be designed for failure.
Containerization and Runtime Sandboxing
Containerization (Docker/Podman) is non-negotiable. It provides the necessary isolation layer.
When running the application, use runtime sandboxing tools like AppArmor or SELinux profiles. These tools enforce mandatory access control (MAC), limiting what system calls the PHP process can make, regardless of what the underlying code attempts.
For instance, if a flaw allows RCE, a properly configured AppArmor profile can prevent the spawned shell process from accessing the /etc/passwd file or initiating outbound network connections, effectively neutralizing the attack payload.
Advanced Mitigation: Dependency Integrity Verification
For maximum security, consider implementing cryptographic integrity checks. While Composer handles basic checksums, you can extend this by:
- Using Private Artifact Repositories: Never allow the build pipeline to pull packages directly from public repositories (like Packagist) during critical builds. Proxy all dependencies through a private, vetted repository (e.g., Artifactory or Nexus).
- Hashing: When a package is approved, hash its entire contents and store that hash alongside the version number. During deployment, verify the downloaded package’s hash against the stored value.
This process ensures that even if the public repository is compromised, your build system will reject the package because the hash will not match the expected, vetted value.
The CI/CD Pipeline Hardening Checklist
| Stage | Security Measure | Goal |
| Pre-Commit | PHP CS Fixer / Pint | Enforce coding standards to prevent “creative” (and potentially risky) syntax. |
| Build | Composer Audit | Use the native composer audit command as a first line of defense before Snyk. |
| Build | Secret Scanning (TruffleHog) | Ensure no .env files or API keys are accidentally baked into the image. |
| Test | SAST (SonarQube/Snyk Code) | Deep-dive into the source code for patterns like SQL injection or Insecure Deserialization. |
| Deploy | Immutable Infrastructure | Deploy as a read-only container filesystem where possible to prevent runtime tampering. |
💡 Pro Tip: When dealing with legacy applications that cannot be fully containerized, consider running the application under a dedicated, unprivileged user account (e.g., nobody) and implementing resource limits (ulimit) to restrict CPU, memory, and file descriptor usage. This severely limits the blast radius of any successful exploit stemming from PHP Composer Flaws.
Conclusion: Vigilance is the Ultimate Patch
The continuous discovery of PHP Composer Flaws underscores a fundamental truth in DevSecOps: security is not a feature; it is a process.
By adopting a layered defense—combining strict dependency pinning, robust containerization, mandatory dependency scanning, and the Principle of Least Privilege—you move from a reactive patching cycle to a proactive, resilient security posture.
For further reading on the technical implications of these vulnerabilities, you can check out the details provided when you read the PHP Composer flaws. Furthermore, understanding the roles and responsibilities in this complex field is critical; we have detailed resources on DevOps roles.