Introduction: There are mistakes you make as a junior developer, and then there are architectural sins that take down an entire enterprise application. Today, I am talking about the latter.
Leaving hardcoded private IPs in your production frontend is a ticking time bomb.
I learned this the hard way last Tuesday at precisely 3:14 AM.
Our PagerDuty alerts started screaming. The dashboard was bleeding red. Our frontend was completely unresponsive for thousands of active users.
The root cause? A seemingly innocent line of configuration code.
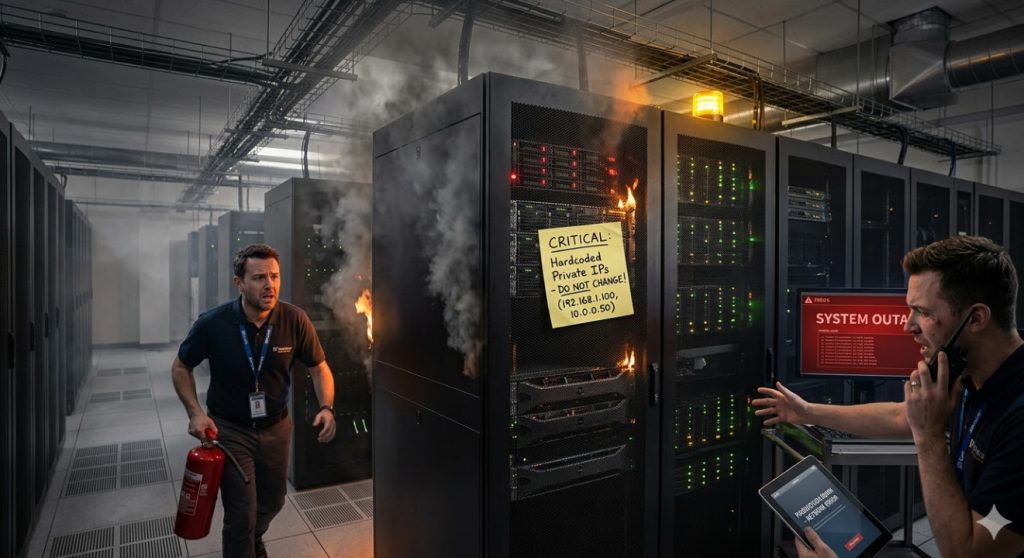
Table of Contents
The Incident: How Hardcoded Private IPs Sneaked In
Let me paint a picture of our setup. We were migrating a legacy monolith to a shiny new microservices architecture.
The frontend was a modern React application. The backend was a cluster of Node.js services.
During a massive late-night sprint, one of our lead engineers was testing the API gateway connection locally.
To bypass some annoying local DNS resolution issues, he temporarily swapped the API base URL.
He changed it from `api.ourdomain.com` to his machine’s local network address: `192.168.1.25`.
He intended to revert it. He didn’t.
The Pull Request That Doomed Us
So, why does this matter? How did it bypass our rigorous checks?
The pull request was massive—over 40 changed files. In the sea of complex React component refactors, that single line was overlooked.
It was a classic scenario. The CI/CD pipeline built the static assets perfectly.
Our automated tests? They passed with flying colors.
Why? Because the tests were mocked, completely bypassing actual network requests. We had a blind spot.
The Physics of Hardcoded Private IPs in the Browser
To understand why this is catastrophic, you have to understand how client-side rendering actually works.
When you deploy a frontend application, the JavaScript is downloaded and executed on the user’s machine.
If you have hardcoded private IPs embedded in that JavaScript bundle, the user’s browser attempts to make network requests to those addresses.
Let’s say a customer in London opens our app. Their browser tries to fetch data from `http://192.168.1.25/api/users`.
Their router looks at that request and says, “Oh, you want a device on this local home network!”
The Inevitable Network Timeout
Best case scenario? The request times out after 30 agonizing seconds.
Worst case scenario? The user actually has a smart fridge or a printer on that exact IP address.
Our React app was literally trying to authenticate against people’s home printers.
This is a fundamental violation of the Twelve-Factor App methodology regarding strict separation of config from code.
Detecting Hardcoded Private IPs Before Disaster Strikes
We spent four hours debugging CORS errors and network timeouts before someone checked the Network tab in Chrome DevTools.
There it was, glaring at us: a failed request to a `192.x.x.x` address.
Never underestimate the power of simply looking at the browser console.
To prevent this from ever happening again, we completely overhauled our pipeline.
Implementing Static Code Analysis
You cannot rely on human eyes to catch IP addresses in code reviews.
We immediately added custom ESLint rules to our pre-commit hooks.
If a developer tries to commit a string matching an IPv4 regex pattern, the commit is rejected.
We also integrated SonarQube to scan for hardcoded credentials and IP addresses across all branches.
The Right Way: Dynamic Configuration Injection
The ultimate fix for hardcoded private IPs is never putting environment-specific data in your codebase.
Frontend applications should be built exactly once. The resulting artifact should be deployable to any environment.
Here is how you achieve this using environment variables and runtime injection.
React Environment Variables Done Right
If you are using a bundler like Webpack or Vite, you must use build-time variables.
But remember, these are baked into the code during the build. This is better than hardcoding, but still not perfect.
// Avoid this catastrophic mistake:
const API_BASE_URL = "http://192.168.1.25:8080/api";
// Do this instead (using Vite as an example):
const API_BASE_URL = import.meta.env.VITE_API_BASE_URL || "https://api.production.com";
export const fetchUserData = async () => {
const response = await fetch(`${API_BASE_URL}/users`);
return response.json();
};
The Docker Runtime Injection Method
For true environment parity, we moved to runtime configuration.
We serve our React app using an Nginx Docker container.
When the container starts, a bash script reads the environment variables and writes them to a `window.ENV` object in the `index.html`.
This means our frontend code just references `window.ENV.API_URL`.
It is infinitely scalable, perfectly safe, and entirely eliminates the risk of deploying a local IP to production.
The Cost of Ignoring the Problem
If you think this won’t happen to you, you are lying to yourself.
The original developer who made this mistake wasn’t a junior; he had a decade of experience.
Fatigue, tight deadlines, and complex microservices architectures create the perfect storm for stupid mistakes.
Our four-hour outage cost the company tens of thousands of dollars in lost revenue.
It also completely destroyed our SLAs for the month.
For more detailed technical post-mortems like this, check out this incredible breakdown on Dev.to.
Auditing Your Codebase Right Now
Stop what you are doing. Open your code editor.
Run a global search across your `src` directory for `192.168`, `10.0`, and `172.16`.
If you find any matches in your API service layers, you have a critical vulnerability waiting to detonate.
Fixing it will take you 20 minutes. Explaining an outage to your CEO will take hours.
Don’t forget to review your [Internal Link: Ultimate Guide to Frontend Security Best Practices] while you’re at it.
Furthermore, ensure your APIs are properly secured. Brushing up on MDN’s CORS documentation is mandatory reading for frontend devs.
FAQ Section
- Why do hardcoded private IPs work on my machine but fail in production?
Because your machine is on the same local network as the IP. A remote user’s machine is not. Their browser cannot route to your local network. - Can CI/CD pipelines catch this error?
Yes, but only if you explicitly configure them to. Standard unit tests often mock network requests, meaning they will silently ignore bad URLs. You need static code analysis (SAST) tools. - What is the best alternative to hardcoding URLs?
Runtime environment variables injected via your web server (like Nginx) or leveraging a backend-for-frontend (BFF) pattern so the frontend only ever talks to relative paths (e.g., `/api/v1/resource`).

Conclusion: We survived the outage, but the scars remain. The lesson here is absolute: configuration must live outside your codebase.
Treat your frontend bundles as immutable artifacts. Never, ever trust manual configuration changes during a late-night coding session.
Ban hardcoded private IPs from your repositories today, lock down your pipelines, and sleep better knowing your app won’t try to connect to a customer’s smart toaster. Thank you for reading the DevopsRoles page!