Introduction
How to login to AWS Management Console with IAM Identity Center(AWS SSO) via a self-managed directory in Active Directory
To use IAM Identity Center(AWS SSO), a self-managed directory in Active Directory to log in to the AWS Management Console, you can follow these general steps:
- Set up an ADFS server: Install and configure ADFS on a Windows server that is joined to your Active Directory domain. This server will act as the identity provider (IdP) in the SAML authentication flow. Refer to create AD server at the link create AD with Windows server 2012-r2
- Enable IAM Identity Center: follow this AWS user guide to configure IAM Identity Center
- Choose your identity source: follow this AWS user guide. Self-managed directory in Active Directory using the below link
- Create a two-way trust relationship (in my case): Create a trust relationship between your AWS Managed Microsoft AD and your self-managed Active Directory domain. Another way you can use AD connecter.
- Attribute mappings and sync your AD user to the IAM identity Center: follow this guided setup of AWS user guide to configure attribute mappings and add users and groups you want(choose the user of Self-managed AD not the user of AWS-managed AD).
- Create an administrative permission set: follow this guide to create a permission set that grants administrative permissions to your user.
- Set up AWS account access for your administrative user: follow this guide to set up AWS account access for a user in the IAM Identity Center.
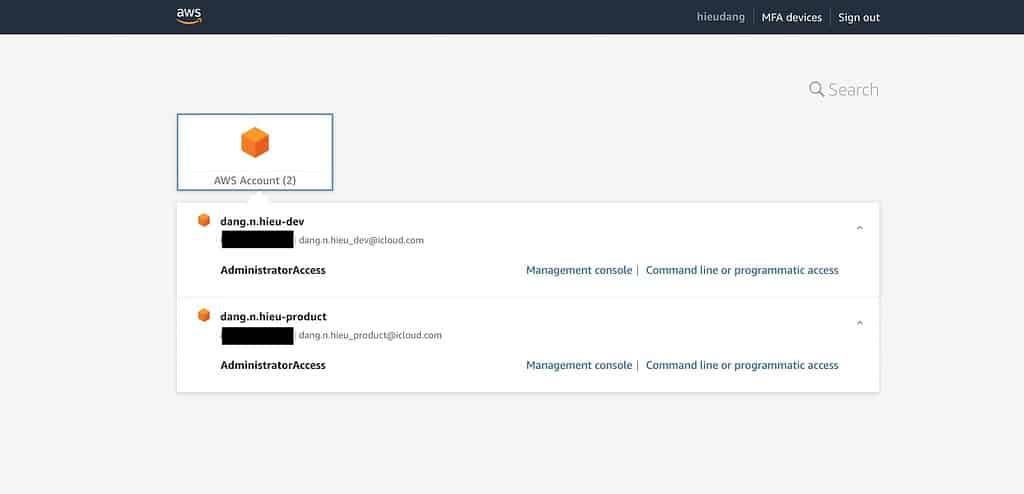
- Sign in to the AWS access portal with your administrative credentials: you can sign in to the AWS access portal by using the credentials of the administrative user that you have already configured.
Using AWS Management Console with IAM Identity Center(AWS SSO)
Using AWS Management Console with IAM Identity Center(AWS SSO) via self-managed directory in Active Directory to log in to the AWS Management Console lab
I tried the lab, so I’ll make a note for everyone:
- The two-way trust relationship step is able fails to verify, you can miss setting Outbound rules for AWS Managed Microsoft AD ENIs, try this to configure the security group.
- Enable the IAM Identity Center with the AWS account root user.
- A single user can access multiple AWS accounts (same organization) from a self-managed directory.
- Sign in to the AWS access portal with your user name, not your user email
Conclusion
Using IAM Identity Center(AWS SSO), a self-managed directory in Active Directory to log in to the AWS Management Console. These steps provide a general overview of the process. The specific configuration details may vary depending on your environment and setup.
It’s recommended to consult the relevant documentation from AWS and Microsoft for detailed instructions on setting up the integration between your ADFS and AWS. I hope will this your helpful. Thank you for reading the DevopsRoles page!
