Table of Contents
Architecting the Ultimate Self-Hosted Bot Management Platform with FastAPI and Docker
In the modern digital landscape, automated threats—from credential stuffing attacks to sophisticated scraping operations—pose an existential risk to online services. While commercial Bot Management Platform solutions offer convenience, they often come with prohibitive costs, vendor lock-in, and insufficient customization for highly specialized enterprise needs.
For senior DevOps, SecOps, and AI Engineers, the requirement is control. The goal is to build a robust, scalable, and highly customizable Bot Management Platform entirely on self-hosted infrastructure.
This deep-dive guide will walk you through the architecture, implementation details, and advanced best practices required to deploy a production-grade, self-hosted solution using a modern, high-performance stack: FastAPI for the backend, React for the user interface, and Docker for container orchestration.
Phase 1: Core Architecture and Conceptual Deep Dive
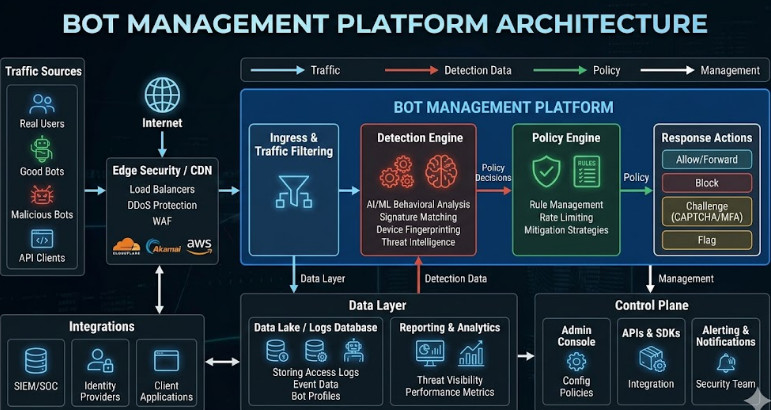
A Bot Management Platform is not merely a rate limiter; it is a multi-layered security system designed to differentiate between legitimate human traffic and automated machine activity. Our architecture must reflect this complexity.
The Architectural Blueprint
We are building a microservice-oriented architecture (MSA). The core components interact as follows:
- Edge Layer (API Gateway): This is the first point of contact. It handles initial traffic ingestion, basic rate limiting, and potentially integrates with a CDN (like Cloudflare or Akamai) for initial DDoS mitigation.
- Detection Service (FastAPI Backend): This is the brain. It receives request metadata, analyzes behavioral patterns, and determines the bot score. FastAPI is ideal here due to its asynchronous nature and high performance, making it perfect for handling high-throughput API calls.
- Persistence Layer (Database): Stores IP reputation scores, user session data, and historical bot activity logs. Redis is crucial for high-speed caching of ephemeral data, such as recent request counts and temporary challenge tokens.
- Presentation Layer (React Frontend): Provides the operational dashboard for security teams. It visualizes attack patterns, manages whitelists/blacklists, and allows for real-time policy adjustments.
The Detection Logic: Beyond Simple Rate Limiting
A basic Bot Management Platform might only check IP frequency. A senior-level solution must implement multiple detection vectors:
- Behavioral Biometrics: Analyzing mouse movements, typing speed variance, and navigation patterns. This requires client-side JavaScript integration (React) that sends behavioral telemetry to the backend.
- Fingerprinting: Analyzing HTTP headers, User-Agents, and browser capabilities (e.g., checking for specific JavaScript execution capabilities).
- Challenge Mechanisms: Implementing CAPTCHA, JavaScript puzzles, or cookie challenges. The challenge response must be validated asynchronously by the Detection Service.
This comprehensive approach ensures that even sophisticated, headless browsers are flagged and mitigated.
💡 Pro Tip: When designing the API contract between the Edge Layer and the Detection Service, always use asynchronous request handling. If the Detection Service is bottlenecked by database queries, the entire platform latency suffers. FastAPI’s async/await structure is paramount for maintaining low latency under heavy load.
Phase 2: Practical Implementation Walkthrough
This phase details the hands-on steps to containerize and connect the core services.
2.1 Setting up the FastAPI Detection Service
The FastAPI backend is responsible for the core logic. We use Pydantic for strict data validation, ensuring that only properly structured requests reach our detection algorithms.
We need an endpoint that accepts request metadata (IP, headers, request path) and returns a risk score.
# main.py (FastAPI Backend Snippet)
from fastapi import FastAPI, HTTPException
from pydantic import BaseModel
import redis.asyncio as redis
app = FastAPI()
r = redis.Redis() # Assume Redis connection setup
class RequestMetadata(BaseModel):
ip_address: str
user_agent: str
request_path: str
session_id: str
@app.post("/api/v1/detect-bot")
async def detect_bot(metadata: RequestMetadata):
# 1. Check Redis for recent activity (Rate Limit Check)
# 2. Run behavioral scoring logic (ML Model Inference)
# 3. Determine risk score (0.0 to 1.0)
risk_score = await calculate_risk(metadata) # Placeholder function
if risk_score > 0.8:
return {"status": "blocked", "reason": "High bot risk", "score": risk_score}
return {"status": "allowed", "reason": "Human traffic detected", "score": risk_score}
2.2 Containerization with Docker Compose
To ensure reproducibility and isolation, we containerize the three main components: the FastAPI service, the React client, and Redis. Docker Compose orchestrates these services into a single, manageable unit.
Here is the foundational docker-compose.yml file:
version: '3.8'
services:
redis:
image: redis:alpine
container_name: bot_redis
ports:
- "6379:6379"
command: redis-server --appendonly yes
backend:
build: ./backend
container_name: bot_fastapi
ports:
- "8000:8000"
environment:
REDIS_HOST: redis
REDIS_PORT: 6379
depends_on:
- redis
frontend:
build: ./frontend
container_name: bot_react
ports:
- "3000:3000"
depends_on:
- backend
2.3 Integrating the Frontend (React)
The React application consumes the /api/v1/detect-bot endpoint. The front-end logic must be designed to capture and package the required metadata (IP, User-Agent, etc.) and send it securely to the backend.
When building the dashboard, remember that the frontend should not only display data but also allow administrators to dynamically update the detection thresholds (e.g., raising the block threshold from 0.8 to 0.9). This requires robust state management and secure API calls.
Phase 3: Senior-Level Best Practices and Scaling
Building the basic structure is only step one. To achieve enterprise-grade resilience, we must address scaling, security, and advanced threat modeling.
3.1 Scaling and Resilience (MLOps Perspective)
As traffic scales, the detection service will become the bottleneck. We must implement horizontal scaling and efficient resource management.
- Database Sharding: If the log volume exceeds what a single Redis instance can handle, consider sharding the data based on geographic region or time window.
- Asynchronous Model Updates: If your risk scoring relies on a machine learning model (e.g., a behavioral classifier), do not load the model directly into the FastAPI service memory. Instead, use a dedicated, containerized ML Inference Service (e.g., running TensorFlow Serving or TorchServe) and call it via gRPC. This decouples model updates from the core API logic.
3.2 SecOps Hardening: Zero Trust Principles
A Bot Management Platform is itself a critical security asset. It must adhere to Zero Trust principles:
- Mutual TLS (mTLS): All internal service-to-service communication (e.g., FastAPI to Redis, FastAPI to ML Inference Service) must be secured using mTLS. This prevents an attacker who compromises one service from easily sniffing or manipulating data in another.
- Secret Management: Never hardcode API keys or database credentials. Use dedicated secret managers like HashiCorp Vault or Kubernetes Secrets, injecting them as environment variables at runtime.
3.3 Advanced Threat Mitigation: CAPTCHA Optimization
Traditional CAPTCHAs are failing due to advancements in AI image recognition. Modern solutions must integrate adaptive challenges.
Instead of a single challenge, the platform should use a “Challenge Ladder.” If the risk score is 0.7, present a simple CAPTCHA. If the score is 0.9, present a complex behavioral puzzle (e.g., “Click the sequence of images that represent a bicycle”). This minimizes friction for legitimate users while maximizing difficulty for bots.
💡 Pro Tip: Implement a dedicated “Trust Score” for every unique user session, independent of the IP address. This score accumulates positive points (successful human interactions) and loses points (failed challenges, suspicious headers). The final block decision should be based on the Trust Score, not just the instantaneous risk score.
3.4 Troubleshooting Common Production Issues
| Issue | Potential Cause | Solution |
| High Latency Spikes | Database connection pooling exhaustion or synchronous blocking calls. | Profile the code using asyncio.gather() and ensure all I/O operations are truly non-blocking. |
| False Positives | Overly aggressive rate limiting or poor behavioral model training. | Implement a “Learning Mode” where the platform logs high-risk traffic without blocking it, allowing security teams to review and adjust the scoring weights. |
| Service Failure | Dependency on a single, non-redundant service (e.g., single Redis instance). | Deploy all critical services across multiple Availability Zones (AZs) and use a robust orchestration tool like Kubernetes for self-healing capabilities. |
Understanding the nuances of these components is crucial for mastering the field. For those looking to deepen their knowledge across various technical domains, exploring different DevOps roles can provide valuable perspective on system resilience.
Conclusion
Building a self-hosted Bot Management Platform is a monumental undertaking that touches every aspect of modern software engineering: networking, security, machine learning, and distributed systems. By leveraging the performance of FastAPI, the portability of Docker, and the dynamic UI of React, you gain not only a powerful security tool but also a deep, comprehensive understanding of scalable, resilient architecture.
This platform moves beyond simple mitigation; it provides deep visibility into the digital attack surface, transforming a costly security vulnerability into a core, controllable asset. Thank you for reading the DevopsRoles page!
